
Chinese Crypto Wallets Face US Treasury Sanctions Over Drug Links
October 12, 2023
Global Response: G20 Nations Band Together to Tackle Crypto Risks
October 14, 2023Unlocking the Secrets: The Crypto Private Key Explained
Unlocking the Secrets: The Crypto Private Key Explained
Cryptocurrencies have triggered a seismic shift in the financial landscape, introducing pioneering solutions for secure, decentralized transactions. At the epicenter of this digital revolution resides the enigmatic realm of cryptographic keys, with the private key taking center stage.
Within the cryptocurrency domain, the private key assumes a pivotal role as an elemental building block, orchestrating the safeguarding of your digital wealth. This article embarks on an odyssey through the intricate realm of crypto’s private keys, illuminating their significance, origins, security paradigms, and beyond.
What is a Private Key in Crypto?
A private key in the world of cryptocurrencies represents a labyrinthine alphanumeric code, akin to a digital fingerprint. It grants its possessor exclusive access and dominion over their digital assets within the sprawling blockchain ecosystem.
This clandestine cipher, resembling a clandestine codebreaker’s treasure map, facilitates a multitude of actions, ranging from orchestrating transactions to gaining entry into wallets and orchestrating the orchestration of one’s crypto portfolio.

Significance of the Private Key
The private key stands as the veritable guardian of security within the cryptocurrency domain, a sentinel with a mandate to uphold the sanctity, validity, and confidentiality of all blockchain transactions. The following elucidates the profound importance of private keys:
Sovereignty and Domination
A private key substantiates one’s rightful ownership of specific cryptocurrency holdings. It’s the virtual counterpart of the golden key that unlocks the vault. Possessing the private key bequeaths full dominion over digital assets, empowering the holder to initiate transfers, receive funds, and administer their crypto kingdom with unbridled authority.
The Impeccable Authorizer
When executing a cryptocurrency transaction, the private key is summoned as the cryptographer’s quill, etching cryptographic signatures onto the transaction. This indelible mark signifies authenticity and carries the imprimatur of the assets’ rightful custodian. Transactions absent this cryptographic seal stand null and void, fortifying the need to safeguard the private key zealously.
The Unyielding Guardian
Private keys serve as an impenetrable bastion of security. Their formidable complexity renders them impervious to brute-force attacks or ingenious hacks. So long as the private key remains concealed, digital assets remain immune to unwarranted intrusion.
The Veil of Anonymity
While blockchain transactions surface on a public ledger, the use of private keys bestows anonymity. Transactions link to wallet addresses rather than personal identities, cocooning user privacy.
How Are Private Keys Conceived?
The genesis of a private key invokes elaborate cryptographic rituals. In most cryptocurrency systems, private keys are birthed through the conjuring of specialized algorithms. The process, although intricate, can be distilled into three phases:
- The Dance of Entropy
Cryptographically sound, random data, referred to as “entropy,” is summoned from diverse sources, such as the capricious dance of your computer’s mouse cursor, the staccato rhythm of keystrokes, and the symphony of system events. This entropy is the inaugural ingredient in the alchemical recipe of key generation. - The Alchemy of Hash Functions
The collected entropy embarks on a transformative odyssey through a one-way hash function. This alchemical metamorphosis transmutes entropy into a fixed-size output—a digital chalice from which the private key shall soon be quaffed. - The Birth of the Private Key
The output of the hash function, bearing the semblance of a labyrinthine cipher, metamorphoses into the private key—a unique, cloaked sequence of characters, shrouded in secrecy and exclusivity. This private key, your digital sigil, is preserved with the utmost sanctity.
A salient caveat:
The generation process must remain enigmatically capricious and unpredictable, akin to the roll of cosmic dice, to fortify the impregnable security of the private key. Any patterns or predictabilities would be akin to a treasure map falling into the wrong hands, beckoning malicious exploiters.
Safeguarding Your Private Key
In the cryptocurrency realm, the security of your private key stands as an unassailable bastion. Surrendering or compromising this guardian can be the harbinger of irrevocable loss. Employing the following safeguards is paramount:
- Embrace the Chill of Cold Storage
For utmost security, consider relegating your private key to the frigid sanctum of a hardware wallet or an offline vault. These “cold storage” sanctuaries are impervious to the sweltering fires of online threats. - Backups as Relics
Maintain resilient backups of your private key. Catastrophic losses can arise from hardware failures or inadvertent erasures. These backups should be sequestered in secure, physical redoubts. - Whisper Not Thy Key
Never part with the secret of your private key. Guard it as the most sacred of oaths. Beware of siren-like phishing attempts and the treacherous seas of scams designed to wrest your key from your grasp. - Lock it with a Cryptographic Key
For software wallets, implement password protection as an added layer of defense. Should an interloper infiltrate your device, this layer of security becomes the guardian at the gate. - Multi factor Authentication
Consider deploying multifactor authentication (2FA) wherever feasible. This sends an oracle’s challenge to anyone attempting to breach your digital fortress. - The Repository of Knowledge
Staying abreast of the latest security threats and practices in the cryptocurrency cosmos is your ever-watchful sentry. Education is your trusted lieutenant in the defense of your digital domain. Loss and Redemption of Private Keys. In the unforgiving realm of cryptocurrencies, the loss of a private key can portend cataclysm. Unlike traditional banking, there exists no “forgot password” recourse. However, avenues of redemption are not entirely impassable:
- The Seed of Resurrection
Many cryptocurrency wallets bestow upon their bearers a lifeline—a seed phrase, a sequence of words birthed during wallet setup. Cling to this phrase, for it holds the key to rekindling your lost private key. - The Benevolence of Wallet Providers
Certain wallet providers extend the olive branch of account recovery services. However, these services typically demand identity verification and might not be universally accessible. - The Cryptographic Cartographers
In the direst of straits, when all hope seems eclipsed, professional assistance from cryptocurrency recovery experts may be the beacon in the tempest. These savants employ diverse techniques to navigate the labyrinthine abyss and restore access to lost wallets.
Diverse Use Cases
Private keys wield influence beyond the mere custody of cryptocurrency. They unfurl as multi-faceted tools in various domains:
- The Virtuoso of Digital Signatures
Private keys orchestrate digital signatures, validating the authenticity of documents, emails, and software in diverse applications. - The Custodian of Access
Within access control systems, private keys stand sentinel, guarding entry to physical realms and digital dominions. - The Arbiter of Identity
In identity verification processes, private keys serve as the rubicon of legitimacy, confirming the bona fides of individuals in online interactions. - The Scribe of Smart Contracts
In blockchain realms like Ethereum, private keys are the quills that pen smart contracts, ushering in self-executing agreements devoid of intermediaries.
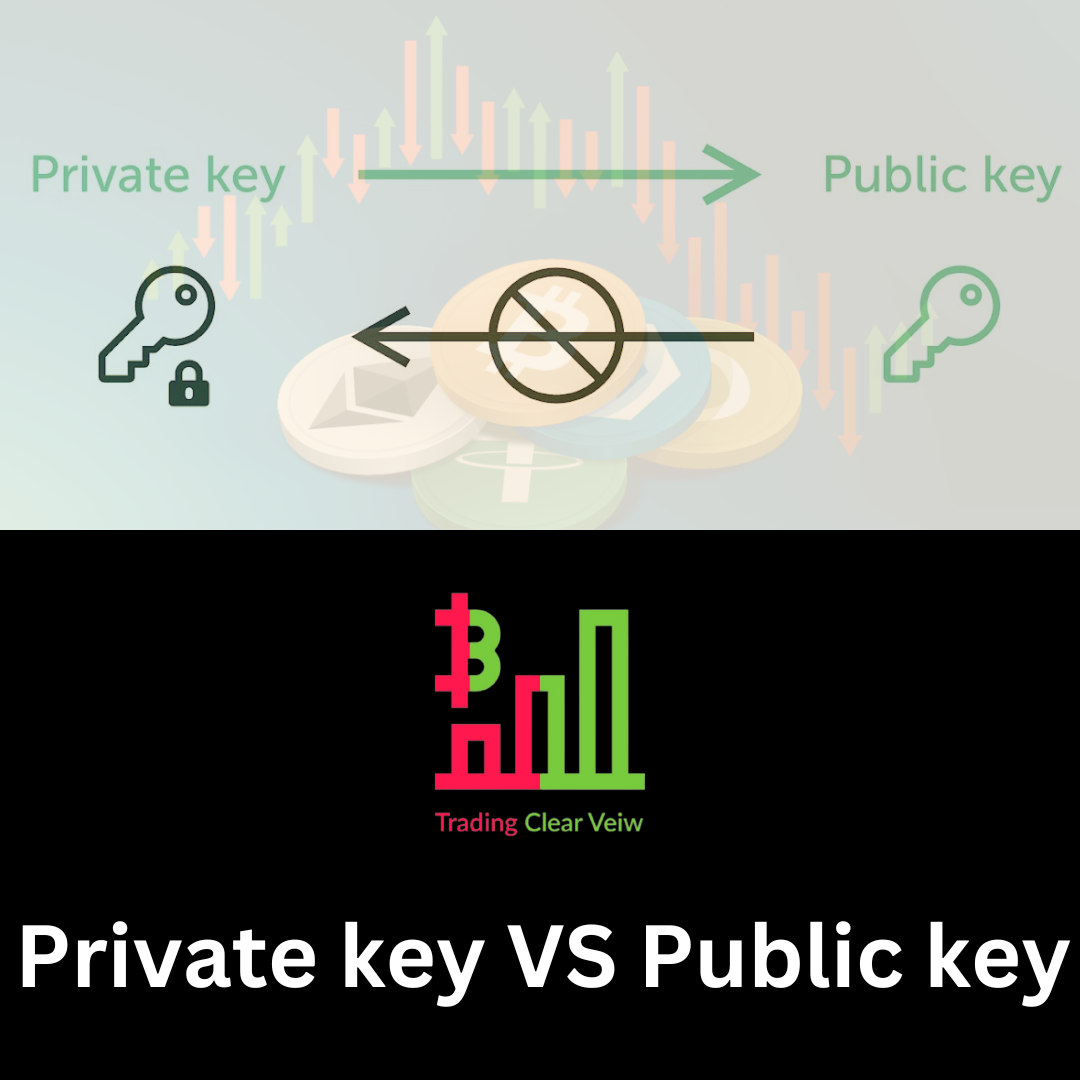
Private and Public Keys
In symphony with private keys, public keys form a harmonious duality within the cryptocurrency tapestry. Derived from private keys, public keys don a different mantle. While the private key remains clandestine, the public key steps into the limelight.
Public keys birth unique wallet addresses, etched indelibly on the blockchain’s public ledger. These addresses act as conduits for others to dispatch cryptocurrency to your wallet. Yet, they remain powerless to access your coffers or undertake unsanctioned endeavors.

Private vs. Public Keys
Private and public keys tread disparate trails within the cryptocurrency ecosystem. Consider their distinctions:
Confidentiality: Private keys are the clandestine warden, never to be divulged, while public keys are open to scrutiny, facilitating cryptocurrency receipts.
Dominion: Private keys vest absolute control over a wallet’s assets, enabling transactions. Public keys remain spectators in this dominion.
Signatory Authority: Private keys wield cryptographic authority, signing transactions as proof of ownership. Public keys bear no such power.
Visibility: Public keys and wallet addresses unfurl on the blockchain, allowing external validation of transactions and balances. In stark contrast, private keys remain concealed, veiled in secrecy.
Private Key Vulnerabilities
Even as private keys stand as the guardians of cryptocurrency security, they are not impervious to lurking threats. A grasp of these vulnerabilities is imperative:
Loss: Accidental forfeiture of the private key begets permanent estrangement from digital assets.
Pilferage: Should malevolent hands seize your private key, your cryptocurrency becomes their plunder.
Phishing: Scammers may deploy cunning stratagems, seeking to entice you into revealing your private key through spurious emails or counterfeit websites.
Malware Menace: Malicious software, if it infiltrates your device, can undermine the fortitude of your private key.
Hacking Havoc: Online exchanges and wallets, while convenient, might serve as breeding grounds for hacking attempts, potentially laying your private key bare.
Sentinel of Safety: Best Practices for Private Key Custodians
To fortify the citadel housing your private key and shield your cryptocurrency treasures, heed these best practices:
Embrace the Cold: For ultimate safeguarding, consign your private key to the glacial embrace of hardware wallets or offline vaults, impervious to online marauders.
Backup Tenfold: Maintain robust backups of your private key, securely stored in physical redoubts. The loss of this key can be cataclysmic.
Secrecy is King: Share not your private key with any soul. It’s a secret reserved for your eyes alone. Beware the sirens of phishing and the beguiling chimeras of scams.
Shield with Passwords: If your sanctuary is a software wallet, enshroud it in the armor of password protection. Infiltrators will find their entry barred.
The Power of Unity: Multifactor Authentication: Contemplate employing multifactor authentication (2FA) wherever plausible, fortifying your defense with this united front.
The Arsenal of Knowledge: Keep yourself apprised of the latest threats and security protocols in the cryptocurrency realm. Education is the sentinel at the gate of your digital fortress.
Loss and Redemption of Private Keys
In the unforgiving realm of cryptocurrencies, the loss of a private key can portend cataclysm. Unlike traditional banking, there exists no “forgot password” recourse. However, avenues of redemption are not entirely impassable:

The Seed of Resurrection: Many cryptocurrency wallets bestow upon their bearers a lifeline—a seed phrase, a sequence of words birthed during wallet setup. Cling to this phrase, for it holds the key to rekindling your lost private key.
The Benevolence of Wallet Providers: Certain wallet providers extend the olive branch of account recovery services. However, these services typically demand identity verification and might not be universally accessible.
The Cryptographic Cartographers: In the direst of straits, when all hope seems eclipsed, professional assistance from cryptocurrency recovery experts may be the beacon in the tempest. These savants employ diverse techniques to navigate the labyrinthine abyss and restore access to lost wallets.
The Citadel’s Guardian
In the world of cryptocurrencies, the private keys is the guardian of sovereignty and security. Grasping its significance, protecting it diligently, and adhering to best practices are imperatives for the safety of your digital assets. Whether you’re a seasoned crypto aficionado or a neophyte, the private key stands at the epicenter of the decentralized financial revolution, a concept deserving of profound comprehension and unwavering vigilance.

